Computers & Technology
mobi, epub |eng | 2017-10-14 | Author:Glenn Fleishman
Safari When you use a web browser, you’re always leaking information about yourself. Use a search engine, and it knows what terms you typed in, what kind of device you’re ...
( Category:
Networking & Cloud Computing
June 27,2020 )
mobi, epub |eng | 2014-06-14 | Author:Steve Baca & John A. Davis
VMware Distributed Power Management This section provides details for configuring and managing VMware Distributed Power Management (DPM). It includes details on concepts, implementation, and management, as well as the steps, ...
( Category:
Certification
June 27,2020 )
mobi, epub |eng | | Author:Unknown
Comprehensions We've already seen a lot of Python's for loop. It allows us to loop over any object that supports the iterable protocol and do something specific with each of ...
( Category:
Computer Science
June 27,2020 )
azw3, epub |eng | 2019-08-19 | Author:David Sim [Sim, David]
01./02. Melbourne, Australia (left) and Rio de Janeiro, Brazil (right). Kiosks in central districts bring a feeling of security to the streets in areas that otherwise lack nighttime population. Integrating ...
( Category:
City Planning & Urban Development
June 27,2020 )
azw3 |eng | 2020-06-14 | Author:Elias Paul & Elias Paul [Paul, Elias]
Chapter 11 Regular expressions So far we have read files, looking for patterns and extracting various sections of lines that we have found interesting. We have used string methods like ...
( Category:
Programming
June 27,2020 )
azw3, epub |eng | 2020-06-14 | Author:Unknown
Traditional EVM metrics like schedule performance index (SPI) and cost performance index (CPI) can be easily translated into agile terms. For example, if the team planned to complete 30 story ...
( Category:
Accounting
June 27,2020 )
azw3, epub |eng | 2020-06-17 | Author:Craig Berg [Berg, Craig]
The first step is to search for the vulnerability exploit. Load the module by using the use command, followed by the full exploit name. The next is to show information ...
( Category:
Hacking
June 27,2020 )
azw3 |eng | 2016-04-06 | Author:Liz Kao & Jon Paz [Kao, Liz]
To clone a case, click the Clone button at the top or bottom of the case record. If it’s the day of a new product or feature release, and many ...
( Category:
Enterprise Applications
June 27,2020 )
azw3, mobi, pdf |eng | 2016-09-07 | Author:Jeremy Watt & Reza Borhani & Aggelos Katsaggelos [Watt, Jeremy]
(5.11) for all . Note that with a two layer neural network basis, we have increased the number of internal parameters which are nonlinearly related layer by layer. Specifically, in ...
( Category:
Electronics
June 27,2020 )
azw3 |eng | 2020-06-15 | Author:Elias Paul [Paul, Elias]
4. REPETITION STRUCTURES So far, everything seen allows us to build pseudocodes that are executed just once, that is, instructions are executed one by one ne sequential until the execution ...
( Category:
Computer Science
June 27,2020 )
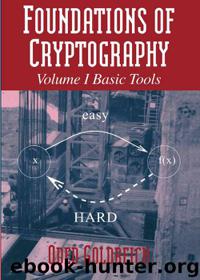
azw3 |eng | 2001-08-05 | Author:Oded Goldreich [Goldreich, Oded]
4.2. Interactive Proof Systems In this section we introduce the notion of an interactive proof system and present a non-trivial example of such a system (specifically to claims of the ...
( Category:
Coding Theory
June 27,2020 )
azw3 |eng | 2020-06-16 | Author:Dave Evans [Evans, Dave]
Figure 13 - CHESS VS. GO BOARD COMPARISON The possible number of first moves in chess is 400 moves (20 white pieces x 20 black pieces). In Go however, there ...
( Category:
Computer Science
June 27,2020 )
epub, mobi |eng | 2020-06-11 | Author:Gabor Szauer [Gabor Szauer]
The IsValid helper function should only return true if at least one of the component tracks stored in the TransformTrack class is valid. For a track to be valid, it ...
( Category:
C++
June 27,2020 )
epub |eng | | Author:Tengfei Liu & Pengpeng Zhang & Zhong-Ping Jiang
( Category:
Management & Leadership
June 27,2020 )
Categories
Popular ebooks
Deep Learning with Python by François Chollet(27917)The Mikado Method by Ola Ellnestam Daniel Brolund(25224)
Hello! Python by Anthony Briggs(24259)
Secrets of the JavaScript Ninja by John Resig Bear Bibeault(23348)
Kotlin in Action by Dmitry Jemerov(22435)
The Well-Grounded Java Developer by Benjamin J. Evans Martijn Verburg(21899)
Dependency Injection in .NET by Mark Seemann(21782)
OCA Java SE 8 Programmer I Certification Guide by Mala Gupta(20645)
Algorithms of the Intelligent Web by Haralambos Marmanis;Dmitry Babenko(19474)
Grails in Action by Glen Smith Peter Ledbrook(18548)
Adobe Camera Raw For Digital Photographers Only by Rob Sheppard(17019)
Sass and Compass in Action by Wynn Netherland Nathan Weizenbaum Chris Eppstein Brandon Mathis(15810)
Secrets of the JavaScript Ninja by John Resig & Bear Bibeault(13659)
Test-Driven iOS Development with Swift 4 by Dominik Hauser(11805)
Jquery UI in Action : Master the concepts Of Jquery UI: A Step By Step Approach by ANMOL GOYAL(11132)
A Developer's Guide to Building Resilient Cloud Applications with Azure by Hamida Rebai Trabelsi(10617)
Hit Refresh by Satya Nadella(9175)
The Kubernetes Operator Framework Book by Michael Dame(8559)
Exploring Deepfakes by Bryan Lyon and Matt Tora(8396)
Robo-Advisor with Python by Aki Ranin(8340)